It’s quick, stealthy and goes unnoticed for long enough to do devastating damage. It’s called text message routing and it’s the sinister cousin of SIM swapping.
SIM swapping or SIM hijacking is switching control of a mobile from one user to another either by porting the target phone number to another SIM, or swapping out one SIM for another. Usually, the criminal bribes or tricks a mobile company employee into making the swap. Bribes can be as little as $100 per SIM swap. If this happens to you, you know something is up because you lose cell service. (Read about T-Mobile’s recent data breach following several SIM swapping attacks, and this shocking story.)
Text message routing or text message forwarding, on the other hand, is where a criminal uses a commercial SMS service—the type businesses use to send out mass SMS to customers—to re-route text messages from a target number to themself. The method is as simple as lying on the required letter of authorization (LOA) that says the signatory has authority to forward texts from one number to another. If this happens to you, you won’t know there’s anything wrong with your phone until you realize you’re not receiving any text messages, or the criminal makes contact. By then a lot of damage can be done.
For both SIM swapping and text message routing, once the criminal has control of the victim’s mobile number, they can access accounts immediately as well as reset passwords on any accounts secured with two-factor authentication, including bank accounts.
Text message routing gained prominence in March after a “hack” by the Chief Information Officer of a company called Okey System, Joseph Cox, who also goes by the pseudonym Lucky225, set out to demonstrate the flaw in telecommunications infrastructure that allows messages to be re-routed with a dishonest LOA (and in this case, no follow up text or call to confirm consent).
Lucky225 used a prepaid card to buy a $16 a month plan with a mass messaging company and completed theLOA with the target phone number. Once the target number was re-routed to a new number, Lucky225 was able to reset the password on all the accounts associated with that number and take over the victim’s life (fortunately, in this exercise, the “victim” was himself).
“This overlooked attack vector shows not only how unregulated commercial SMS tools are but also how there are gaping holes in our telecommunications infrastructure, with a hacker sometimes just having to pinky swear they have the consent of the target,” Joseph/Lucky225 said of the attack. While he used a specific service to carry out his attack, he says: “The carrier doesn’t matter. It’s basically the wild west.”
Prior to Joseph Cox’s “hack”, text message routing had not received much coverage. But it’s now more prominently on the radar as a relatively effortless and cheap way to take over a victim’s phone number to steal their money and disrupt their life. As this author notes: “This is much easier than SMS hijacking, and causes the same security vulnerabilities. Too many networks use SMS as an authentication mechanism.”
Lucky225 points out that thousands of these unregulated mass messaging services exist: “There are a plethora of wholesale VoIP providers that let you become a reseller with little to no verification, many of them allow blanket Letters of Authorization (LOAs), where you as the reseller promise that you have an LOA on file for any number you want to text enable for your resellers or end-users,” Lucky225 said.
He quotes Allison Nixon, Chief Research Officer at Unit221B, a New York City-based cyber investigations firm, as saying: “It’s time for federal regulators to step up and protect consumers,” and Eva Galperin, Director of Cybersecurity at the Electronic Frontier Foundation, as commenting that this “hack” “underscores the importance of moving people off of SMS 2FA and, more broadly, off of ‘login with your phone number’ solutions.”
So, what’s a mobile user to do? Respected security commentator Brian Krebs says, “Phone numbers were never designed to be identity documents, but that’s effectively what they’ve become. It’s time we stopped letting everyone treat them that way.” He advises users to:
- Rethink how your use your phone number.
- Remover your phone from all accounts where possible and use a mobile app to generate any one-time codes for multi-factor authentication.
- Avoid selecting SMS or phone calls for second factor or one-time codes.
- Secure any online accounts you value with a unique and strong password, as well the most robust form of multi-factor authentication available.
- Remove your phone number from any email accounts you have and use a robust second factor for all account recovery options.
The FBI has this advice on how to defend against SIM swapping, and Europol offers this advice.
How MySudo can help
These sorts of phone takeover attacks happen because people tend to use their personal phone number for everything they do online and off. By using MySudo, you can protect yourself against SIM swapping and text message routing and other forms of cyberattack by creating separate Sudos for all your interactions.
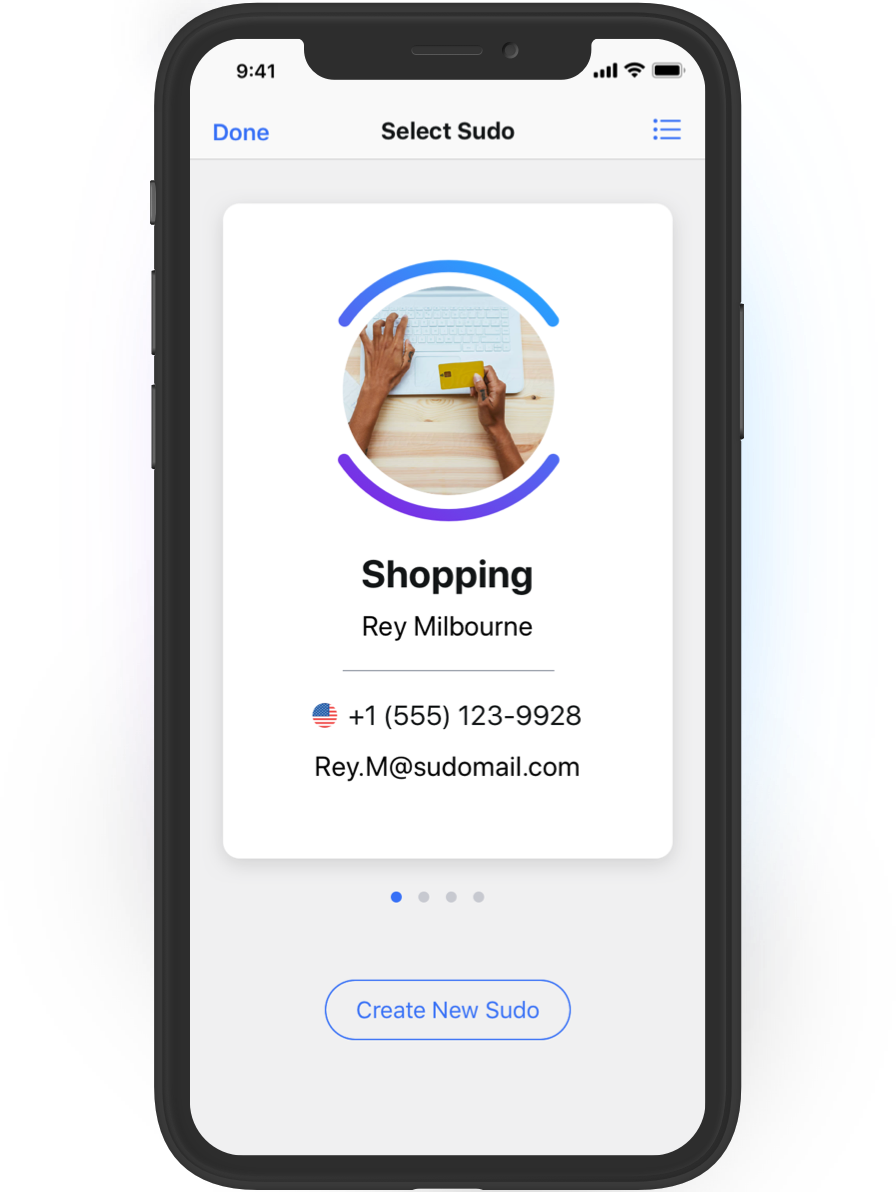
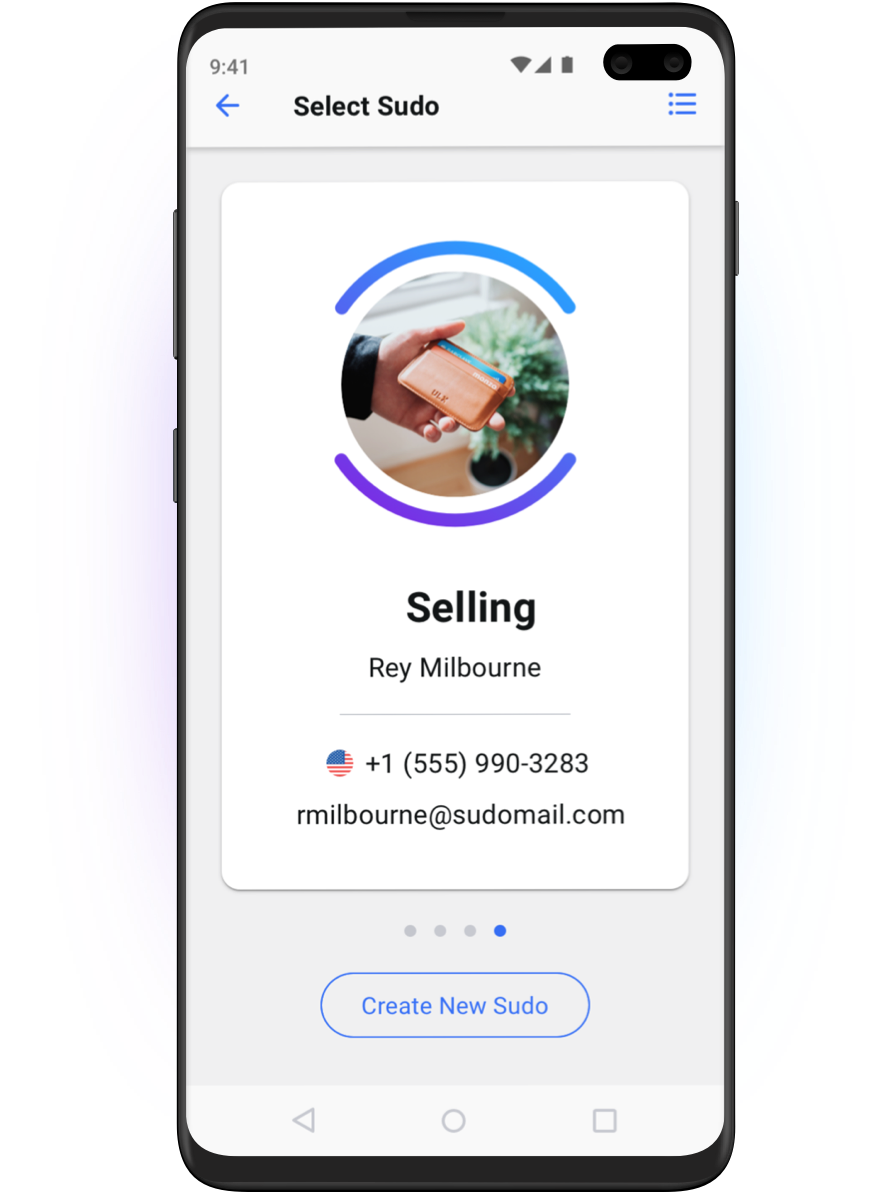
A Sudo is a secure, customizable digital identity or ‘profile’ that intentionally differentiates from your personal identity and protects your personal data. A Sudo isn’t a ‘burner’ or fake ID—it’s a real, alternative identity that you can use anywhere your personal identity is required. Your Sudo profile is a secure stand-in for yourpersonal identity, and it’s entirely under your control.
In MySudo, a user can create up to nine Sudos and each one can have its own set of attributes and associated capabilities:
- name
- phone number
- address
- email address
- virtual cards for secure shopping
- private browser (all your bookmarks and any cookies that sites set are compartmentalized to the browsing Sudo)
- notification settings for phone, email and message
- contacts and more…
You give each of your Sudos one or more identity attributes that are different from your personal identity. Youcan make your Sudo identity a little different (e.g. by having a different phone number) or very different (e.g. by having a different name, email address, phone number, virtual cards, contacts, etc.). You label each Sudo and can even assign a different notification sound to each, to alert you to the context of the incoming contact (is it my kid’s soccer coach or my bank is calling or messaging, for instance).
Importantly, you structure your Sudos to achieve the degrees of privacy, safety, organization and convenience you need. For example, you might regard your medical information as more sensitive than your financial information, and your financial information as more sensitive than your contacts. You decide what suits you.This is called compartmentalization and it’s the most powerful data privacy strategy there is.
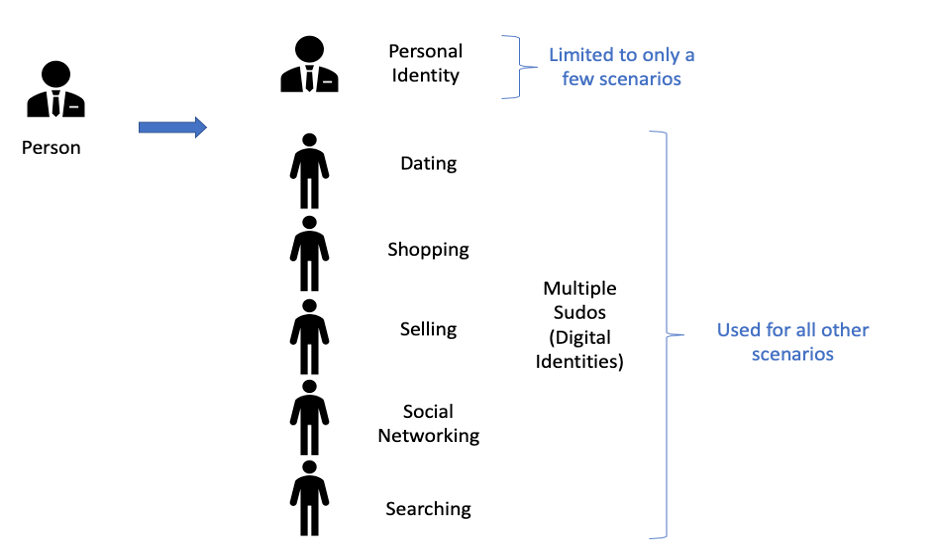
So now you have up to nine different phone numbers to use in different scenarios, and so the impact of a phone takeover or other type of cyberattack like a data breach is greatly reduced. You could also create a dedicated ‘Multi-factor auth’ Sudo for only receiving authentication codes for logging into your accounts.
Learn more about what MySudo offers and all the ways it protects your data and identity.
Photo by Nathan Dumlao on Unsplash