Living in a highly connected digital world has its risks. Having your personal information caught up in a data breach is a big one.
We talked about data breaches here , and these are the takeaways:
- A data breach is a security event where highly sensitive, confidential or protected information is accessed or disclosed without permission or is lost.
- Organizations, governments and individuals can be victims of data breaches.
- 3.5 billion people had records exposed in the 15 biggest data breaches of this century. In just the first half of 2019, data breaches exposed 4.1 billion records.
- Verizon reports 70% of data breaches in the past year were perpetrated by external actors; 45% of breaches featured an intentional effort to subvert a system’s security; and 22% of breaches were caused by errors.
- Data breaches can expose your highly sensitive personally identifiable information or PII. PII isn’t only email and passwords; it’s any data that can be used to identify you.
Now, down to business. If your personal information has been caught up in a data breach, here are some steps to take:
Immediate steps
- Understand which site or service was breached and what data of yours could have been contained in the data breach. This may help you to focus your energies, to avoid privacy fatigue.
- Change your password on the site or service that was compromised. This helps if the breach is confirmed or suspected to contain passwords.
- If the site or service supports multi-factor authentication and you have not already enabled it, now is a good time to do it.
Next steps
- If you may have used the same or similar password on other sites too, change your password on those sites. Generate unique passwords for each site and manage them using a password manager.
- Review your account profile on the affected site or service and see what you can do to reduce the impact if the breached data was used to access your account. This could include:
- Reduce the personal information in your account profile to the bare minimum required by the service.
- Use alternate information for data elements such as answers to the secret questions and date of birth. Most non-government sites don’t need your real data of birth; they just want something to match against when speaking to you on the phone, so choose any date of birth and answers to secret questions and store those details with your login information in your password manager. Or use MySudo (see later).
These two suggestions are actions you can take to minimize the available data if the same service were to be breached again or the attackers were continuing to exfiltrate data. There’s a degree of “closing the gate after the horse has bolted” about this, but if you don’t take this action on the affected service now, you may forget or be less likely to do it once the incident has passed. This is simply good general practice, and this minimization approach on all the sites and services you use is even better because it becomes a preventative measure for the future.
Future-proofing steps
- Going forward, we recommend you use unique, generated passwords for each site you access.
- Data breaches containing personal information also help criminals to craft and send more specific and compelling phishing emails. Continue to scrutinize your email messages and the links in them before clicking.
- Some data breaches contain personal information that is enriched from public sources, such as profiles on social networking sites like Twitter, LinkedIn, Facebook and Instagram. Periodically review your accounts on these sites to make sure your choices for each of the privacy and security settings continue to match how you want to share or not share your personal information.
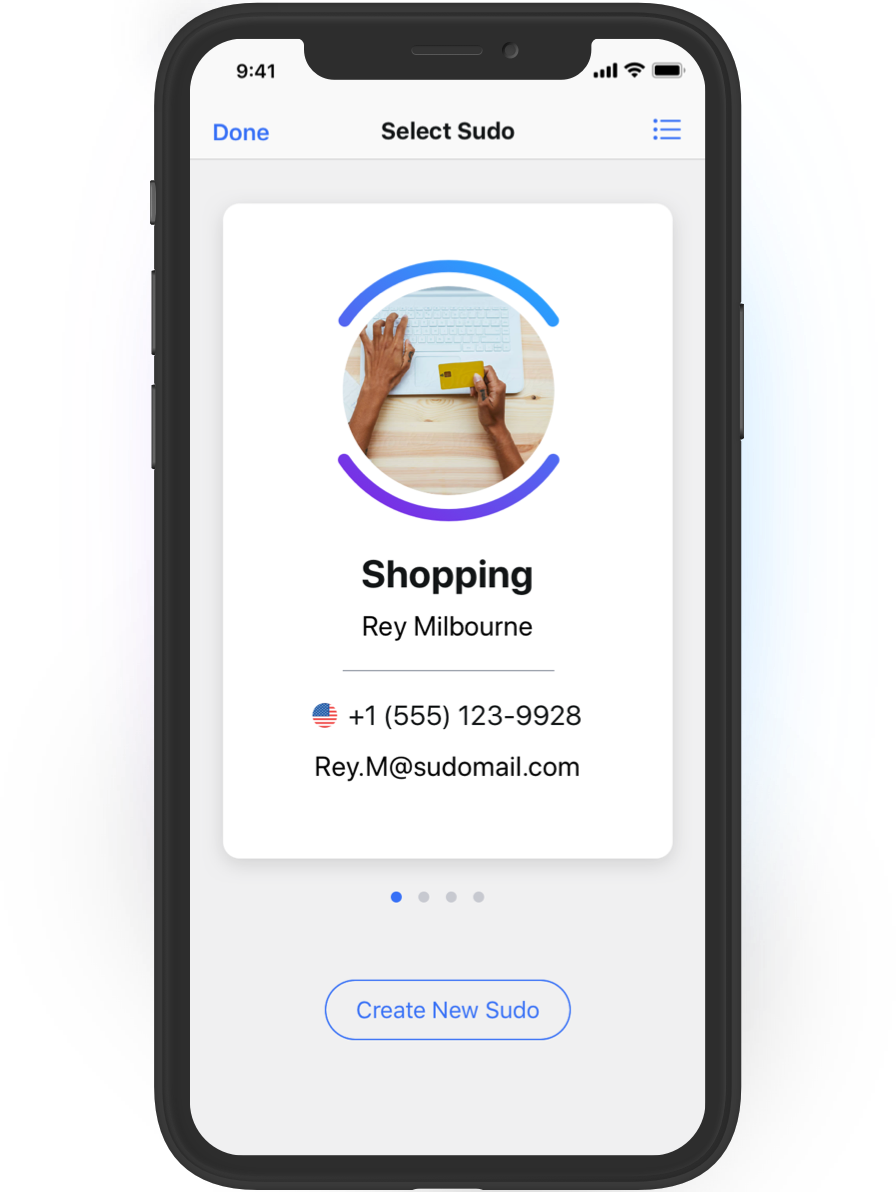
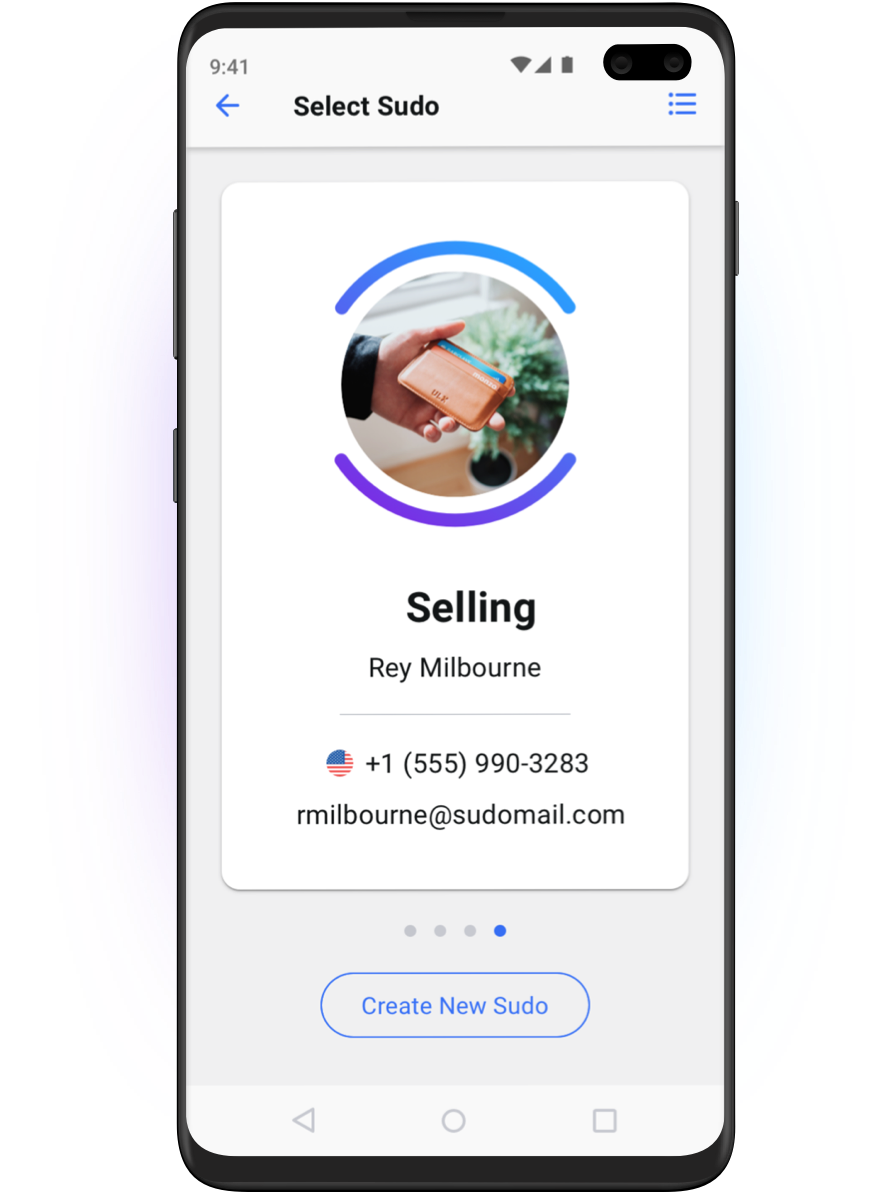
- Switch to MySudo app to protect your personal information: phone numbers, email, messaging, browsing history and online payments. Watch our 90-second video to discover the world’s only all-in-one privacy solution.
MySudo makes compartmentalization simple. You’re probably aware that compartmentalization means categorizing and separating your private data to spread the risk and reduce the impact when it is compromised. Compartmentalization is the world’s most powerful data privacy strategy, and MySudo was created on the exact same principle.
No two data breaches are the same, but following these steps will help you to manage the impact on you from the current data breach and do all you can to minimize the impact of a data breach in future.