Statistically, you’re a sitting duck for cyberattack during COVID-19.
ZDNet research reports since the start of the pandemic:
- a 40% increase in unsecured remote desktop computers
- brute force attacks on remote desktops increasing by 400% during March and April 2020
- email scams skyrocketing by 667% in March 2020
- 90% of the nearly 5 billion COVID-19 related web pages being found to be scams
- over half a million Zoom credentials for sale on the dark web and a 2000% increase in malicious files with ‘Zoom’ in the name
- a 72–105% spike in ransomware linked to COVID-19.
As of May 2020, the US Federal Trade Commission (FTC) had received 60,000-plus reports of fraud related to COVID-19 and individual losses from these scams totaled around $44 million. The FTC says most scams relate to travel/vacations, online shopping and health care. People working from home and college students are also targets. Scammers impersonating public health authorities is a common trick, where criminals claim to be conducting contact tracing for COVID-19 and ask for personal information or send a malicious link via text to the victim. The US Federal Trade Commission has published advice on how to recognize and deal with COVID-19 scams.
As a consumer and possibly a remote worker, you’re at serious risk of privacy breaches or cyberattack from at least three different angles as the world struggles to contain the deadly virus and work and live in a new normal:
- the inadvertent or deliberate exposure and misuse of your personal data collected at cafes, gyms and other venues to support contact tracing
- inappropriate access to corporate data, via unsecured networks and devices you might be working on
- COVID-19 case reporting data being shared by health organizations and others, including employers, accidentally identifying you in the process.
What’s the risk with contact tracing?
Contact tracing is the process of gathering information about the people with whom a confirmed case of COVID-19 might have been in contact, and the places they have been. The WHO regards contact tracing as a critical weapon in the fight against COVID-19, and most countries around the world are using it in some form, with varying degrees of success.
Contact tracing can be done manually or with technology. Manual contact tracing is the pen and paper or QR code approach you’ve likely seen in your local bars and restaurants. Technology assisted contact tracing (TACT) includes apps such as Australia’s COVIDSafe, Canada’s ABTraceTogether, and Germany’s Corona-Warn-App.
But largely it’s not the government developed or sanctioned contact tracing apps that leave people exposed and at risk so much as the casual and ad hoc collection of personal data at hospitality and other venues to support contact tracing efforts. This type of data collection is highly distributed across many small operations and is being conducted by people with little to no training in handling personal data.
Most commonly, these venues ask you to scan a QR code and submit your details at a web site, or to write your contact details, including name, phone number, email address and residential address, as well as time of visit, on to a single sheet of paper or a log that sits in a common area such as on a counter or at a central checkpoint within the venue.
The problems are obvious: your personal information may be left exposed, fall into the hands of those who don’t know how to securely manage and store it and who may use it for nefarious purposes, or be sold to companies that want to spam you.
Experts in the UK are warning of a “mass violation of rights” after some companies reportedly sold the customer data collected by pubs and restaurants on to third parties such as marketers, credit companies and insurance brokers. One firm even explains in its privacy policy that it may use personal data to “make suggestions and recommendations to you about goods or services that may be of interest to you” and share it with third parties including “service providers or regulatory bodies providing fraud prevention services or credit/background checks.” It may also “collect, use, store and transfer” records of access to certain premises including “time, ID number and CCTV images”.”
Also in the UK, there are reports of some venue staff using the personal information to harass patrons, and of data being used in scam contact tracing activities in an attempt to defraud patrons. New Zealand and Australia report similar data concerns. COVID-19 scams are a growing global problem. The IAPP reports: “COVID-19 has proven to be one of the most effective phishing lures of recent years, as epidemics and health scares tend to provide fertile ground for social engineering attacks.”
What’s the risk with remote work?
Criminals are capitalizing on lower defenses and vulnerabilities caused by the widespread and rapid shift to remote work, especially in companies whose business functions were not previously performed remotely. There’s variable, often outdated, security arrangements in place for the massive conduit that now exists between corporate or cloud and home networks and the myriad connected devices. People globally are focused on fighting the pandemic and stemming its devastating death toll. There’s heightened anxiety as people struggle to live and work in the ‘new normal’.
Put simply, criminals capitalize on vulnerability. The main motivation for these attacks is always the same: financial gain and massive disruption. Criminals want to trick people into giving them access to sensitive data and/or funds and exposing credentials that would allow them to infiltrate corporate information and payment systems. Attacks bring down services, and often open the floodgates for more criminal activity. And it’s incredibly easy for criminals to achieve. As PwC says: “As has been proven time and time again, it only takes one. One click, one missing endpoint agent, one failed alert, one unsuspecting employee, and the adversary can proclaim victory over your network.”
What’s the risk with COVID-19 case data sharing?
The issue here is loss of privacy. Re-identification of data is easier than people think because anonymization of data sets is more difficult than people think.
The International Association of Privacy Professionals (IAPP) warns: “… organizations should … be cognizant that sharing the names of people who have had or recovered from COVID-19 presents a privacy risk for them. Even if that data is anonymized before being shared, the risk of re-identification and subsequent privacy harms can remain.”
So what can you do?
The best way to stay private and safe online is to not share your personally identifiable information (PII) in the first place. Of course this isn’t always possible, as in the case of your data being shared by a health organization or your employer during the pandemic. But MySudo is a useful tool in your personal privacy toolkit for almost all other interactions you have online and off. It’s the only app on the market that offers private and secure phone, email, browsing and payments all in one place, with functionality to use these privacy capabilities via Sudos—secure digital profiles that work as real, alternatives to your personal information.
See how MySudo works:
In addition to using MySudo instead of your personal information online, there are important steps you can take to spot and avoid COVID-19 scams. The FTC has a web page of advice, which includes:
- Do not respond to texts, emails or calls about checks from the government.
- Ignore offers for vaccinations and home test kits.
- Hang up on robocalls.
- Watch for emails claiming to be from the CDC or WHO.
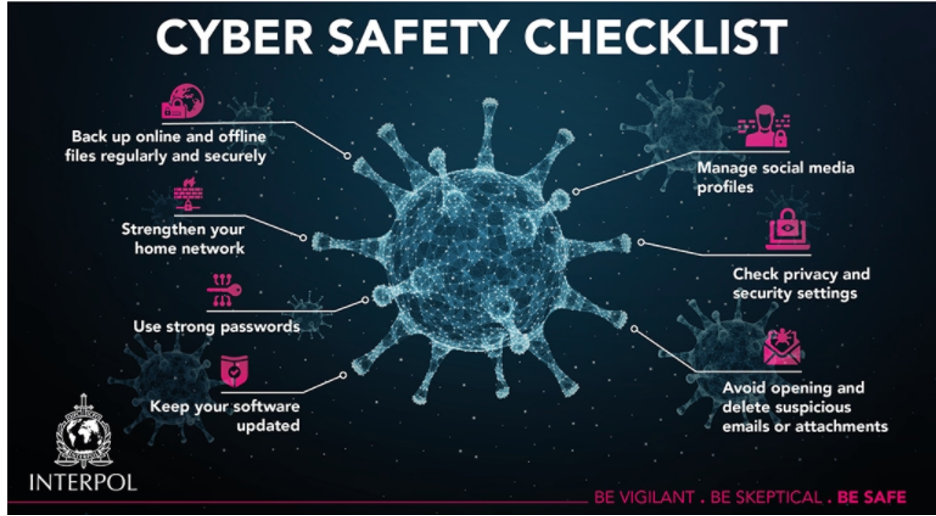
Interpol has this handy infographic:
PwC has advice for remote workers too, which includes being skeptical of emails from unknown senders, not forwarding suspicious emails to co-workers, and reporting suspicious emails to the IT or security department. See more.
At Anonyome Labs, the makers of MySudo consumer app and Sudo Platform business toolkit, we’re creating a world in which people have exclusive control and freedom over their private information. We’re changing the privacy and security paradigm—and resolving the greatest challenges business and consumers face. There’s never been a better time.
Photo by 🇨🇭 Claudio Schwarz | @purzlb