Data privacy is subjective and complicated, but it definitely does matter – and more so every year as cybersecurity threats increase and a federal privacy law remains a pipedream in the United States.
“More and more data about each of us is being generated faster and faster from more and more devices, and we can’t keep up. It’s a losing game both for individuals and for our legal system. If we don’t change the rules of the game soon, it will turn into a losing game for our economy and society,” says Brookings Institution global thought leader on privacy, AI and cross-border challenges in information technology, Cameron F. Kerry.
The IAPP defines data privacy as, “the right to have some control over how your personal information is collected and used.” But why does control matter? What’s the big deal if a company knows your name and address because they sent you the parcel you ordered? Or if Big Tech can track you across web sites and build a profile of you based on your browsing history?
We’ll give you 9 good reasons why data privacy matters.
1. Privacy is a fundamental human right.
Privacy is addressed in all the major human rights instruments, including the United Nations Declaration of Human Rights 1948, Article 12, and in the constitutional statements of around 130 countries. Protecting your fundamental right to privacy means you can:
- limit others’ control over you, to know about you and to cause you harm
- better manage your professional and personal reputations
- put in place boundaries and encourage respect
- maintain trust in relationships and interactions with others
- protect your right to free speech and thought
- pursue second chances for regaining your privacy
- feel empowered that you’re in control of your life.
2. Web sites and services collect personal data about you — much of it highly sensitive.
Unsurprisingly, every company in business wants to sell you their products and services. To have the best chance of landing the sale, they want to know as much information about you as possible so they can personalize ads (more on that later) and target their sales push.
But a lot of the personal data that web sites and services collect includes some of the most personal and highly sensitive information you possess, including your name, SSN, home address, telephone numbers, what property you own, login details, personal opinions posted anywhere, criminal records, life events such as divorce, and every single purchase you make.
This data tracking and collection is called surveillance capitalism, which drives what’s known as the data economy. Professor Emerita Shoshana Zuboff of Harvard Business School first defined surveillance capitalism as, “the unilateral claiming of private human experience as free raw material for translation into behavioral data. These data are then computed and packaged as prediction products and sold into behavioral futures markets — business customers with a commercial interest in knowing what we will do now, soon, and later.”
3. Businesses use the personal data to personalize ads and online experiences.
Personalized ads rely on the invasive surveillance of your personal data we’ve just covered. And while it’s true that some consumers want a personalized online shopping experience because it might save time and money and enhance their online experience, it’s also true that, increasingly, consumers don’t want personalization or hyper-personalization when it comes at the expense of their privacy. Only 21% of US consumers want apps to track them across the internet for targeted advertising under Apple’s new App Tracking Transparency (ATT) feature, for instance.
The ad personalization process known as real-time bidding is fraught with significant data privacy issues:
- Hundreds of businesses get access to a user’s data
- Most anyone can participate in process, and while there are penalties for misusing bid stream data, parsing the data is still highly valuable to participants.
- Bid stream data can be harvested even without third party cookies so recent efforts by Apple and Google to ban third party cookies do nothing to mitigate the privacy risks.
- The bid stream data is usually anonymized but it’s relatively easy to match a user to their information.
- Data brokers readily package the bid stream data (particularly valuable location data) and sell it to other businesses and even governments with little oversight.
This last point has some commentators particularly worried since they see personalized advertising as a national security risk in addition to a personal privacy risk.
4. Businesses also use personal data to set higher prices, control the content you see, and influence your purchasing and even political decisions.
Every action you perform online has become a piece of data which is used to coerce and constrain your digital experiences. You see it in the ads that show up across all your devices after an Internet search, in the ever-narrower set of content you’re shown on your social media sites, and in the increasingly compelling, and sometimes spooky, product recommendations you receive.
Web sites and services track your behavior, particularly your repeated behavior, such as frequent location, hotel and flight searches, and use the data to increase the price at a future date since they know you are interested and more likely to make a purchase.
And of course the Facebook Cambridge Analytica scandal is a great case study of how personal information can be breached and used to influence political decisions.
The cherry on top for businesses is they can use all this consumer data to improve their own product offerings and supply chains.
5. Data brokers are worse than the companies who collect the data.
Data brokers aggregate and package up personal data and sell it for huge profit too.
Data brokers are businesses that harvest, manipulate and even misrepresent consumer data and sell it to businesses, usually for marketing purposes. Data brokers are legitimate but unregulated businesses, there are about 4,000 of them worldwide, and their industry is worth about US $200 billion annually.
Many of the brands and businesses that you interact with and buy from see your data as an additional lucrative product they can sell to others for profit. Around 1,500 leading brands sell the data from their customer loyalty programs, and that data can go into many different databases. Some of these brands are Google and Facebook, and even banks.
Once data brokers have the information, they sell it, usually in list form. Your email address on a list of people with a particular medical condition such as diabetes would be worth about $80 and on a list of a particular class of traveler about $250.
6. Even governments can see what you are doing online.
Governments do request access to personal data held by the private sector, and it’s the subject of much regulatory debate and consumer concern. In 2019 66% of US adults said they believe they face more potential risks than benefits from government data collection.
The OECD says, “Unlimited government access to personal data held by the private sector, including for stated national security reasons, negatively impacts trust in the digital economy, creating uncertainty with adverse market effects,” but acknowledges that “data flows across borders are integral to the global digital economy and a necessary input for reaping the benefits of digitalisation.”
The ideal is to put in place appropriate governance and safeguards for trusted governments access to personal data held by private entities, which is on the OECD’s agenda.
7. Some businesses use dark patterns to maximize the data they gather.
Dark patterns are intentional user experience features of websites and apps designed to make it harder for you to do what you want, either through complexity or deception.
Think of dark patterns as traps to get more of your personal information and to tempt you into buying products and services.
The motivation for trapping users online is profit, either directly through a purchase or indirectly through data sharing, which is at the root of surveillance capitalism as we said. The more information a brand has about its users, the better they can target their audiences with tailored content in the hope they’ll buy.
Find out more about common dark patterns.
Australia’s Competition and Consumer Commission also just pointed out that the lack of choice in device settings such as a pre-installed search engine (by the all-powerful Google) is another way tech giants quietly assume control over consumer data.
8. Stored personal data can be caught in a data breach.
A data breach is a security event where highly sensitive, confidential or protected information is accessed or disclosed without permission or is lost. Organizations, governments and individuals can be victims of data breaches, and usually these events are enormously costly in terms of time, money or corporate reputation.
To give you an idea of the size and scale of some data breaches, 3.5 billion people had records exposed in the 15 biggest data breaches of this century. In just the first half of 2019, data breaches exposed 4.1 billion records.
Data breaches can occur accidentally (e.g. someone inside an organization inadvertently accesses and views information, or devices containing sensitive information are stolen or lost) or purposefully (e.g. someone inside an organization purposefully accesses and/or shares information with malicious intent, or criminals use sophisticated means such as phishing emails, brute force attacks and malware to exploit weaknesses in networks or individual behavior). Read the top 5 security concerns this year.
As of 2019, the World Economic Forum put cyberattacks in the top five risks to global stability. Worldwide, more than 80% of cyberattacks come from phishing emails, which deliver 94% of malware. In the first six months of 2019, attacks on Internet of Things devices (one of the fastest-growing emerging technologies) tripled, and malware attacks that leverage applications already installed on a system (known as fileless attacks) increased by 256%.
Often victims of data privacy breaches aren’t aware they’re a victim or they find out too late, and they don’t know the person or company violating their right to privacy. Find out how a criminal carries out a data breach and what to do if you’re caught in one.
9. Criminals can use the stolen credentials to commit crimes like credit card fraud and identity theft. The dark web is thriving.
Internet-connected computers are attacked every 39 seconds in the US and data is often traded on the dark web, an intentionally hidden part of the Internet where cybercrime flourishes.
According to Deloitte in most cases, criminals won’t use the data themselves but are either engaged by a third party to obtain the data or plan to sell the information on the dark web. Buyers from the dark web may use the data for financial theft from credit cards, to create fake passports and identities, transfer money between accounts, resell stolen information at a higher price to the media, or other illicit activities.
The COVID-19 pandemic is worsening cybercrime.
What you can do to protect your data privacy
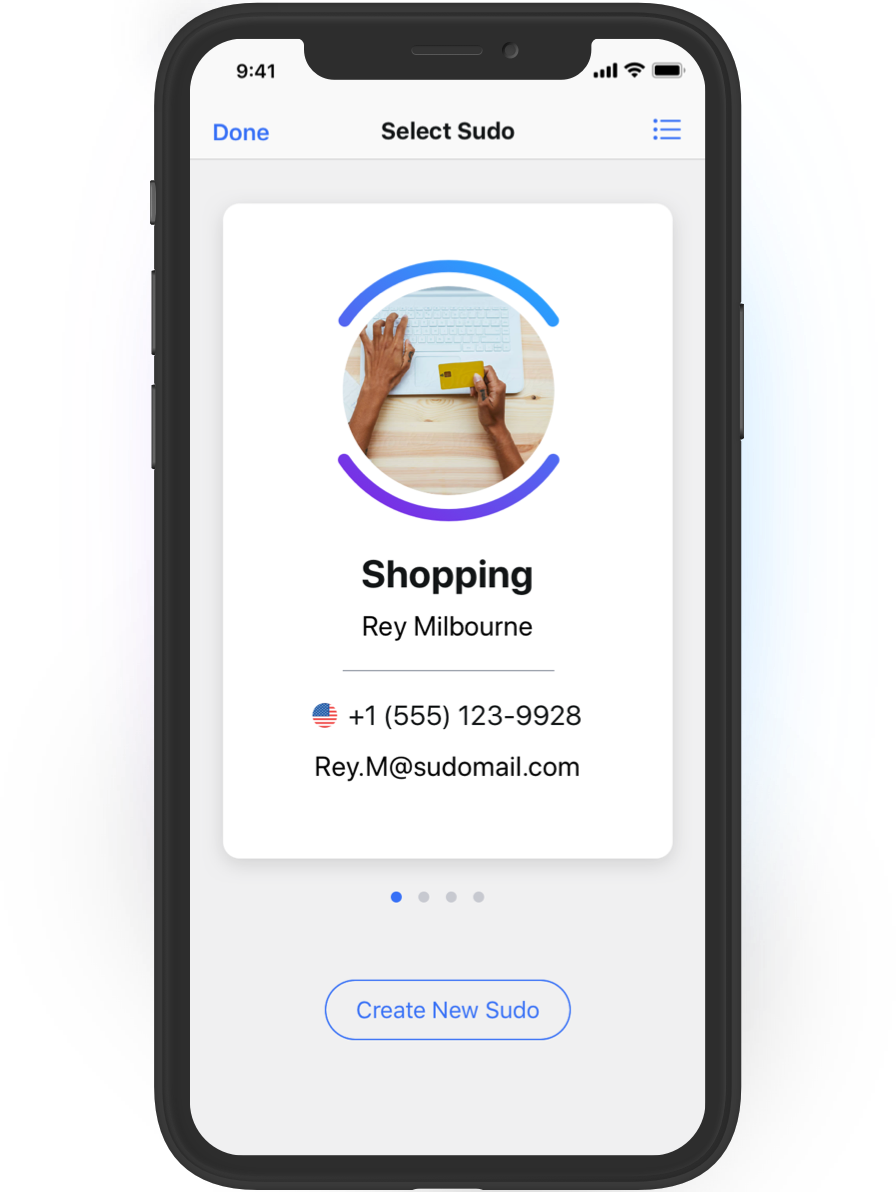
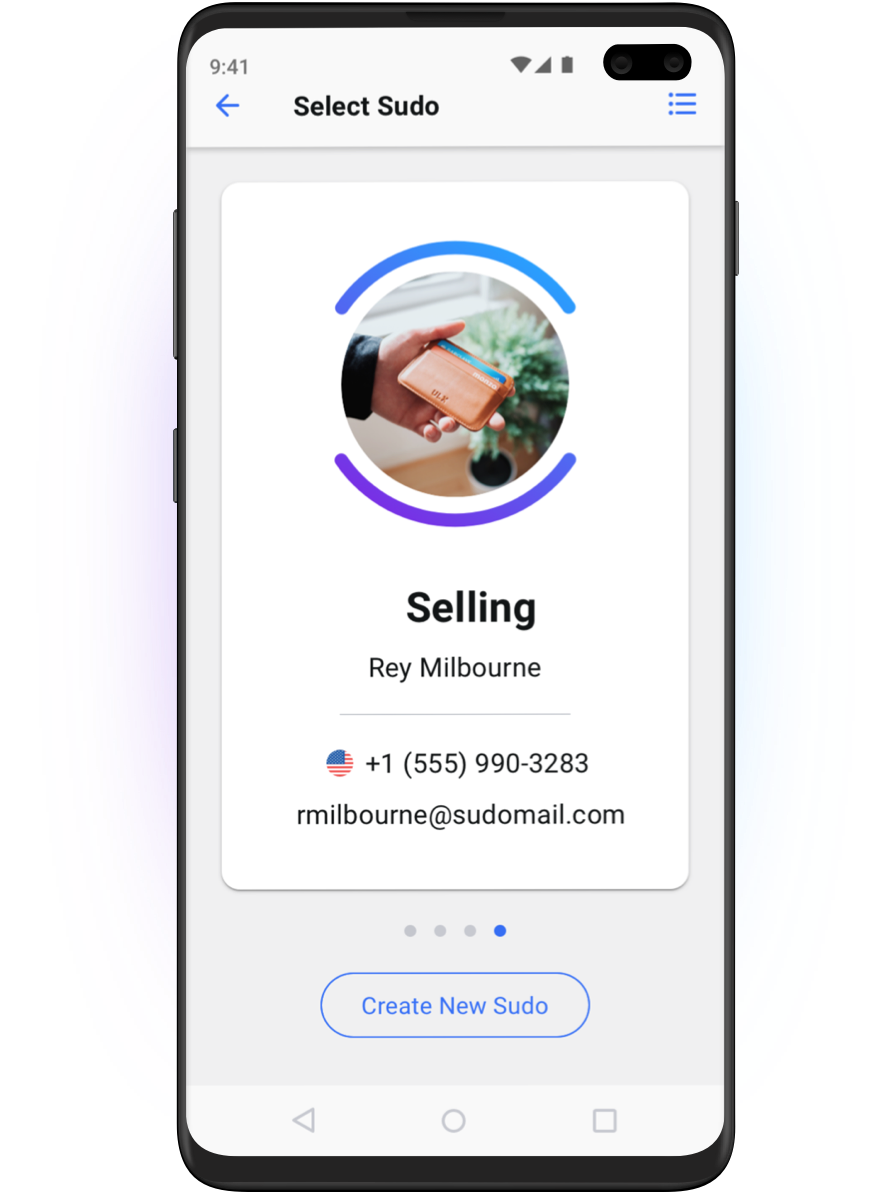
Anonyome Labs, the makers of MySudo, believes being private doesn’t mean opting out of online services or hiding from the world. We empower people to be able to determine what information they share, and how, when, where and with whom they share it.
MySudo is the world’s only all-in-one privacy app, full of privacy and security features. Download the app and then take 90 seconds to learn how to use it. Until data privacy is better protected by the companies who collect, the governments who access it, and the legal system, we all need proactive tools like MySudo.