Phishing is a common type of scam aimed at stealing personal information from victims. The techniques phishers employ are becoming more sophisticated and varied. Considering this, it is important that anyone who uses the internet — or even just has a phone — understands the more advanced strategies that phishers might use, such as “spear phishing.”
What Is a Spear Phishing Attack?
Spear phishing is most commonly done through electronic communication mediums, such as email. It establishes a single target, which may be an individual or may be a specific group, like a company. If the target is a single, especially lucrative target like a CEO, it is called “whale phishing” or a “whaling attack.” The scammers will then find all of the information they can on the target, and use this information in order to sound legitimate and trick the target into divulging more valuable information, such as credit card numbers, passwords, or company strategies.
Commonly, the scammer will pretend that they are someone the victim knows, like their manager, in order to convince them to answer their questions or follow their malicious links. This may even mean that anyone who is accustomed to answering to authority figures — such as a child — is at higher risk of falling victim to a spear phishing scam.
Spear Phishing vs Phishing
While most phishing schemes involve sending the same bait to as many people as possible, spear phishing employs a targeted approach. The goal of average phishing schemes is to potentially catch a few victims in a wide net, whereas spear phishing narrows the focus onto a smaller, but more potentially lucrative target. Spear phishing is far more difficult due to the information-gathering process, but it is also more effective, and presents a higher reward when it is successful.
Spear Phishing Examples
There are actually several high-profile cases of spear phishing scams that had devastating results. These cases often show all of the hallmarks of common spear phishing tactics: specific targeting, impersonation, and theft of private information.
Ubiquiti Networks
In 2015, Ubiquiti Networks, an affluent computer networking company, reported that they had lost $47 million as the result of a spear phishing scam. The company said that the investigation showed no evidence of intentional sabotage from within the company. Rather, a spear phishing attack on their finance department resulted in the transfer of funds from a subsidiary company in Hong Kong into the third party bank accounts of the scammers.
As in many cases like this, the information needed to transfer the funds was gained by impersonating known business associates. Additionally, the FBI published a public advisory in 2015 warning that business activities involving wire transfers to foreign bank accounts are especially at risk of spear phishing scams. According to the advisory, the losses attributed to scams such as spear phishing amounted to roughly $200 million in 2014.
Snapchat
In 2016, the personal information of several Snapchat employees was compromised as the result of a spear phishing scam where the scammer posed as Snapchat’s CEO. Although no funds or other information appeared to have been stolen, Snapchat did have to spend resources on protecting employees and ex-employees from identity fraud as a result of the leak.
Protecting Yourself Against a Spear Phishing Attack
Spear phishing is generally more successful than phishing, largely due to the effort involved. This also means that it can be more difficult to protect oneself or (or one’s company) from it. Basic phishing tactics often (but not always) suffer from the same failings as most catch-all scams: poor spelling, vague wording, and generally suspicious behavior. These red flags are relatively easy to spot. Avoiding spear phishing is a bit more tricky.
- Read messages carefully. Scammers want to catch you off guard. Always be on the lookout for suspicious emails.
- Don’t assume messages are from who they say they are. Phishers commonly impersonate others, especially people with authority, in order to get the information they want.
- Be wary of particularly urgent messages. Scammers don’t want you to have time to think about the message.
- Don’t give out private information. Unless you are absolutely certain about another person’s identity and their authorization to have certain information, never give out private information.
- Be careful of links. Links can lead you to webpages with phishing software. Keep an eye out for link shorteners or other link cloaking methods.
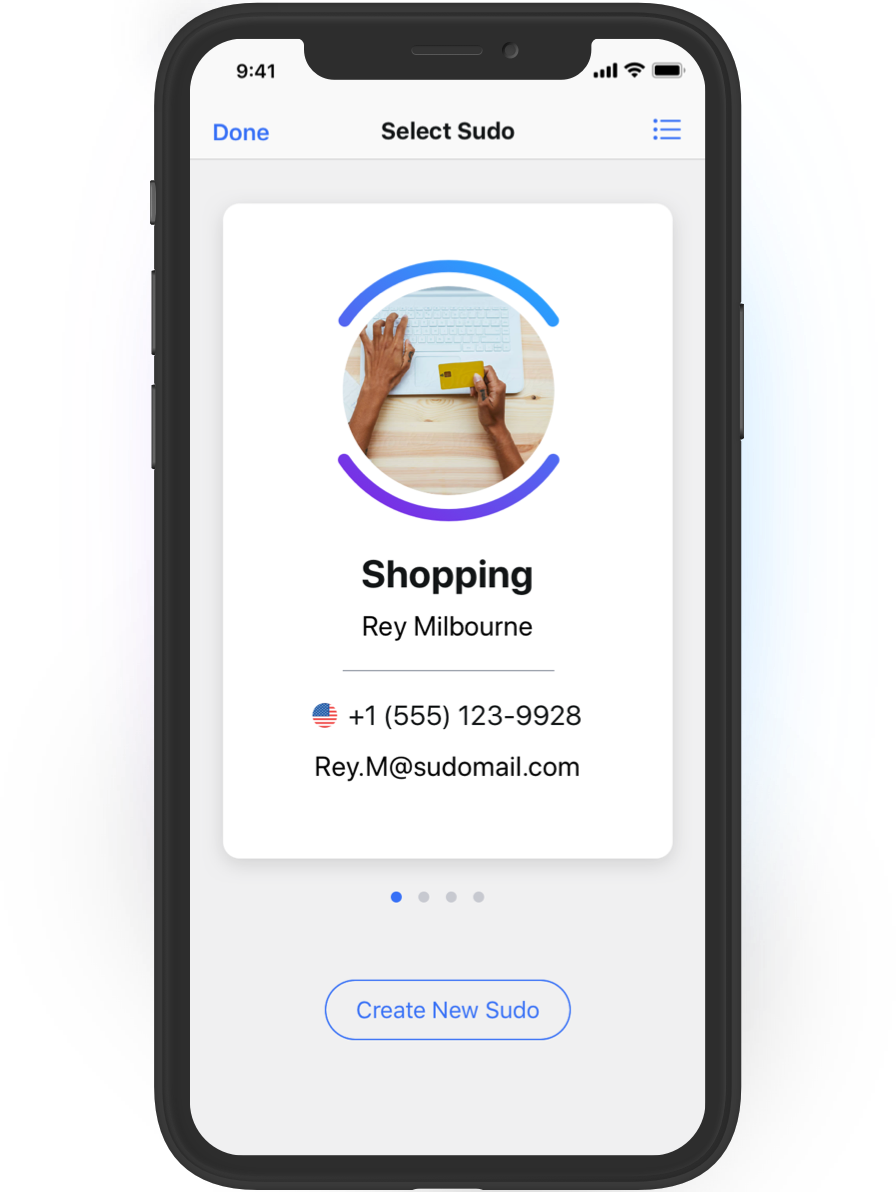
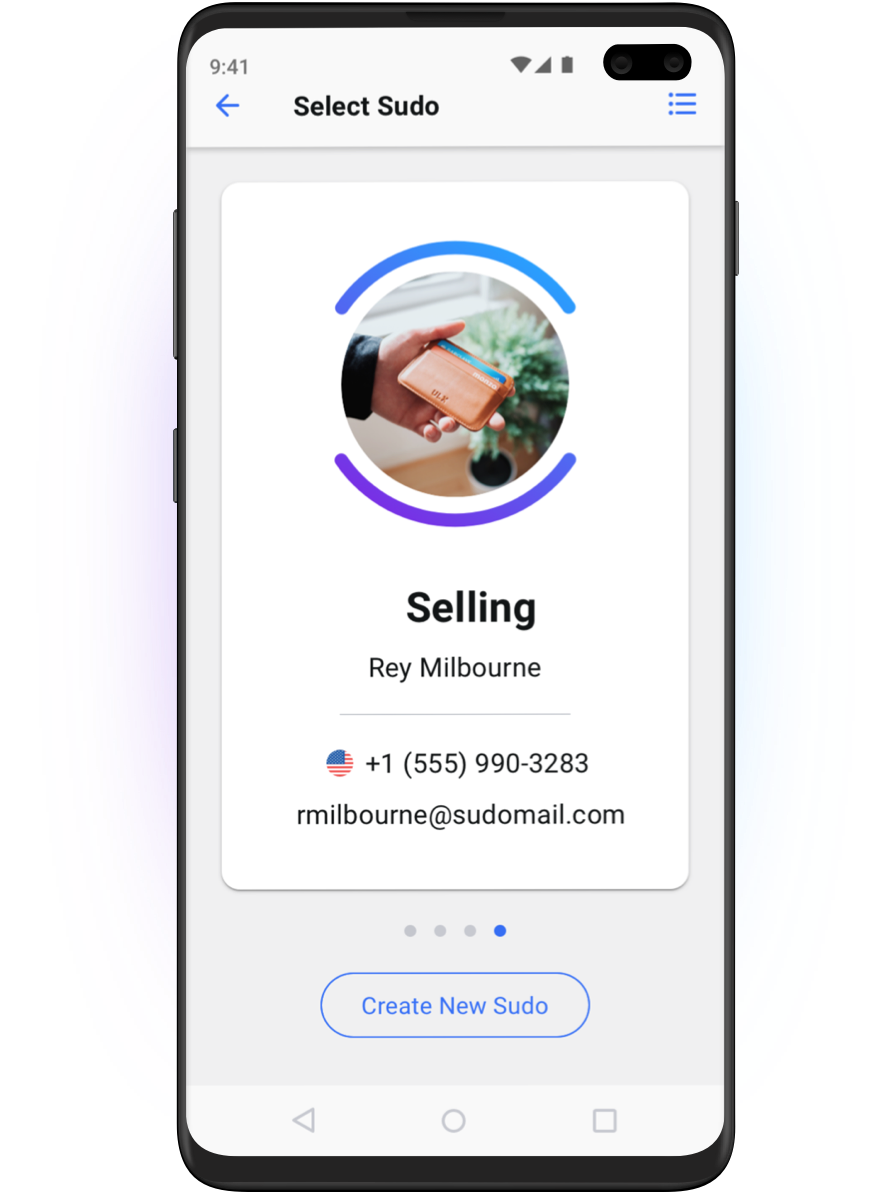
- Don’t use real personal information. Phishers can’t use information maliciously if it isn’t real information. In response to more sophisticated phishing scams, services like MySudo are being developed which provide their users with dummy profiles and even alternate contact methods. This allows people to navigate the internet without using any private information.
Image by Clker-Free-Vector-Images from Pixabay